Reliability
We check your IT infrastructure and your system architecture for fail-safety (single point of failure, redundancy).
Threats to your IT systems are lurking everywhere, with attacks coming from both inside and outside your organization. Attackers are usually one step ahead, so the vulnerability of systems and the functionality of IT security measures can only be confirmed by regular testing. Through targeted examinations, we detect weak areas and recommend appropriate options for optimization.
We check your IT infrastructure and your system architecture for fail-safety (single point of failure, redundancy).
We analyze your network and identify vulnerabilities inside and outside (e.g. firewall rules).
We evaluate the adequacy and effectiveness of your IT security measures (e.g. detection, countermeasures).
We carry out targeted attacks on your IT systems and expose open ports and vulnerabilities.
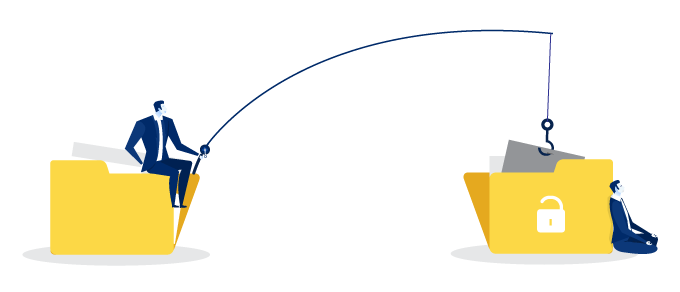
We send confidence-inspiring emails to your employees and mimic deceptive landing pages to elicit sensitive information.

The number of so-called phishing attacks is increasing sharply – with sometimes very well forged messages via e-mail or SMS, attackers try to lure your employees to target landing pages in order to enter sensitive information (e.g. passwords) or download malicious code. We recreate such attacks and evaluate the success rate to raise awareness among your employees. Then we assist you in selecting the appropriate security measures.